TeamViewer QuickSupport is a remote control application that allows users to connect to another computer or device and provide technical assistance. This software is commonly used by IT professionals, support technicians, and individuals who need remote access to their devices. While TeamViewer QuickSupport offers convenience and efficiency, it is important to consider the security features and risks associated with using this software.
One of the key security features of TeamViewer QuickSupport is its use of encryption. Encryption is the process of converting data into a secure format, making it difficult for unauthorized individuals to access or interpret. TeamViewer QuickSupport uses 256-bit encryption, which is considered one of the most secure methods available. This ensures that the data transmitted during a remote control session is protected from interception or tampering.
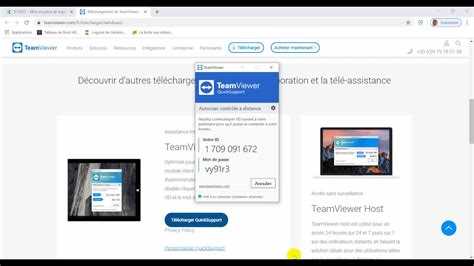
Another security feature of TeamViewer QuickSupport is the ability to set up secure connections using a unique ID and password. When connecting to a remote device, users must enter a unique ID and password provided by the device owner. This adds an additional layer of security, as only individuals with the correct credentials can establish a connection. Furthermore, the password is generated randomly for each session, reducing the risk of unauthorized access.
Despite these security features, it is important to be aware of the potential risks associated with using TeamViewer QuickSupport. One risk is the possibility of phishing attacks. Phishing involves tricking individuals into providing sensitive information or downloading malicious software by impersonating a legitimate entity. Attackers may send emails or messages claiming to be from TeamViewer and asking for login credentials or personal information. It is important to verify the authenticity of such communication to avoid falling victim to phishing attempts.
Additionally, there have been reports of unauthorized access to TeamViewer QuickSupport sessions. In some cases, attackers have gained remote access to users’ devices by exploiting vulnerabilities in the software or by accessing devices with weak passwords. It is crucial to regularly update the software and use strong, unique passwords to minimize the risk of unauthorized access.
In conclusion, while TeamViewer QuickSupport offers convenience and useful features for remote control, it is important to understand and mitigate the associated security risks. By employing strong passwords, regularly updating the software, and being cautious of phishing attempts, users can make the most of TeamViewer QuickSupport while keeping their devices and data secure.
Is TeamViewer QuickSupport safe?
TeamViewer QuickSupport is generally considered a safe and secure remote desktop software solution. It offers various security features to protect users’ data and privacy. However, like any software, there are potential risks to be aware of.
Here are some of the security features of TeamViewer QuickSupport:
- End-to-end encryption: TeamViewer uses AES-256 encryption to secure the remote connection between the devices involved in the session. This encryption ensures that the data transmitted during the session remains private and cannot be intercepted.
- Two-factor authentication: Users can enable two-factor authentication for their TeamViewer accounts, adding an extra layer of security by requiring a unique verification code in addition to their password.
- Access control: Users have full control over who can access their computer remotely using TeamViewer QuickSupport. They can configure access permissions and set up whitelists to allow only trusted individuals or devices to connect.
- Session recording: TeamViewer QuickSupport allows session recording, giving users the ability to keep an audit trail and review the actions performed during a remote session. This can help identify any suspicious activity.
However, there are potential risks when using TeamViewer QuickSupport:
- Phishing attacks: Attackers may try to exploit users by sending fake emails or messages that mimic TeamViewer support. It is essential to be cautious when responding to requests for remote access and ensure they come from legitimate sources.
- Weak passwords: Weak passwords can be exploited by attackers attempting to gain unauthorized access to TeamViewer accounts or the remote device itself. Users should always choose strong, unique passwords and consider enabling two-factor authentication.
- Unsecured devices: If the remote device running TeamViewer QuickSupport is not adequately protected, it can pose a security risk. Ensure the device has up-to-date security software, strong passwords, and is kept physically secure.
In conclusion, while TeamViewer QuickSupport offers strong security features such as end-to-end encryption and access control, users should also take precautions to minimize the risks associated with remote desktop software. By following best practices such as using strong passwords, enabling two-factor authentication, and verifying the legitimacy of remote access requests, users can enhance the safety of their TeamViewer QuickSupport sessions.
Discover the security features
TeamViewer QuickSupport is equipped with a range of security features to ensure the safety and privacy of its users. These features include:
- End-to-End Encryption: TeamViewer QuickSupport uses end-to-end encryption to protect all data transmitted between the remote and local devices. This means that even if the data is intercepted, it cannot be deciphered without the encryption keys.
- Multi-Factor Authentication (MFA): TeamViewer QuickSupport supports MFA, which adds an additional layer of security by requiring users to provide multiple forms of identification, such as a password and a temporary code sent to their mobile device.
- Access Control: TeamViewer QuickSupport allows users to control who can access their device. Users can set up permissions and restrictions to ensure that only authorized individuals can establish a remote connection.
- Permissions Management: With TeamViewer QuickSupport, users have control over what actions the remote user can perform on their device. They can specify the level of access, such as view-only or full control, and can revoke permissions at any time.
- Audit Logging: TeamViewer QuickSupport keeps a detailed log of all remote sessions, including the actions performed, session duration, and the identities of both parties involved. This log can be used for auditing and troubleshooting purposes.
These security features help to mitigate potential risks and ensure that confidential information remains protected during remote support sessions. However, it is important for users to follow best practices, such as using strong and unique passwords and keeping their operating systems and software up to date, to further enhance the security of their devices.
Understand the potential risks
While TeamViewer QuickSupport provides remote access and support capabilities, it is important to understand the potential risks associated with its use. These risks include:
- Unauthorized access: If the TeamViewer QuickSupport application is installed on a device without the user’s knowledge or consent, it can enable unauthorized access to sensitive information and files.
- Privacy concerns: The remote access capabilities of TeamViewer QuickSupport can potentially compromise user privacy if misused or abused by malicious individuals or organizations.
- Exploitation of vulnerabilities: Like any other software, TeamViewer QuickSupport may have vulnerabilities that can be exploited by attackers to gain unauthorized access or control over devices.
- Social engineering attacks: Attackers can use social engineering techniques to trick users into granting access to their devices through TeamViewer QuickSupport, potentially leading to unauthorized remote access and data theft.
It is important for users to be cautious when using TeamViewer QuickSupport and to take steps to mitigate these risks, such as:
- Only download from trusted sources: Ensure that you are downloading TeamViewer QuickSupport from the official TeamViewer website or other reputable sources to avoid downloading tampered or malicious versions.
- Verify the identity of the supporter: Before granting remote access to your device, verify the identity and legitimacy of the person requesting access. Do not provide access to anyone you do not trust or who cannot prove their identity.
- Use strong passwords: Protect your TeamViewer account and devices with strong, unique passwords to minimize the risk of unauthorized access.
- Keep the software updated: Regularly update the TeamViewer QuickSupport software to ensure you have the latest security patches and bug fixes.
- Monitor remote access: Keep an eye on any remote access sessions initiated through TeamViewer QuickSupport and terminate them if you suspect any suspicious activity.
By understanding the potential risks and taking necessary precautions, users can use TeamViewer QuickSupport in a more secure manner and minimize the chances of falling victim to unauthorized access or privacy breaches.
Encryption and authentication
TeamViewer QuickSupport provides strong encryption and authentication measures to ensure the security of remote sessions. Here are some key aspects:
-
Encrypted Data Transmission: TeamViewer QuickSupport utilizes AES (Advanced Encryption Standard) 256-bit encryption, which is considered highly secure. This encryption is used to protect data transmitted between the remote computer and the local device, ensuring that all information remains confidential.
-
End-to-End Encryption: All communication between the remote computer and the local device is encrypted using end-to-end encryption. This means that the data is encrypted on the sender’s side, transmitted securely, and then decrypted on the receiver’s side. This process ensures that only the intended recipients can access and understand the transmitted data.
-
Two-Factor Authentication: TeamViewer QuickSupport supports two-factor authentication, adding an extra layer of security to the remote access process. With two-factor authentication enabled, users need to provide both their password and a unique verification code sent to their mobile device before accessing a remote session.
-
Access Control: TeamViewer QuickSupport allows the participant (the person providing support) to control the level of access they grant to the remote device. The participant can choose to grant full control, view-only access, or restrict certain actions, ensuring that they have complete control over the remote session.
-
Identity Verification: TeamViewer QuickSupport provides identity verification measures to ensure that only trusted individuals have access to remote devices. Participants can use email invitations or random meeting IDs to initiate a remote session, and the local device owner needs to authorize the connection before it can be established.
Overall, TeamViewer QuickSupport prioritizes data security by implementing strong encryption and authentication measures. Users can feel confident that their remote sessions are protected from unauthorized access and that their data remains confidential during the support process.
Two-factor authentication
Two-factor authentication (2FA) is an additional layer of security that can be enabled for TeamViewer QuickSupport. It adds an extra step to the login process, requiring users to provide two pieces of evidence to verify their identity.
The first factor is usually something the user knows, such as a password or PIN. The second factor is something the user possesses, such as a smartphone or hardware token. These two factors combined significantly enhance the security of the login process and help prevent unauthorized access.
When two-factor authentication is enabled, users logging in to TeamViewer QuickSupport will be prompted to enter their username and password as usual. After successful entry, they will be prompted to provide the second factor, which can be a one-time password (OTP) generated by an authentication app, a text message verification code, or a physical token.
Enabling two-factor authentication adds an extra layer of protection against unauthorized access to TeamViewer QuickSupport. Even if an attacker manages to obtain a user’s password, they will still need the second factor to gain access. This significantly reduces the risk of account compromise.
By implementing two-factor authentication, TeamViewer QuickSupport aligns with industry best practices for enhancing security. It makes it much more difficult for attackers to impersonate legitimate users and gain unauthorized access to sensitive information or systems.
However, it is important for users to choose a strong password and protect their second factor (such as a smartphone) to ensure the effectiveness of two-factor authentication. Additionally, users should be cautious of phishing attempts that may try to trick them into providing their login credentials and bypassing the two-factor authentication process.
In conclusion, two-factor authentication is a valuable security feature that can be enabled in TeamViewer QuickSupport. It provides an additional layer of protection against unauthorized access and enhances the overall security posture of the application.
Session recording and auditing
TeamViewer QuickSupport does not offer session recording as a built-in feature. This means that any screen sharing or remote control sessions cannot be recorded directly within the TeamViewer QuickSupport software.
However, it is possible for users to record their screens using third-party software or screen recording tools. In such cases, the recording would be done by the user themselves, rather than by TeamViewer. It is important to note that when using third-party software, users should ensure that the software they choose is reputable and safe.
In terms of auditing, TeamViewer QuickSupport does not offer specific auditing functionalities. However, it is possible to monitor the sessions taking place on a device by checking the session logs in the administrative settings of the operating system. These logs may include information such as the time and duration of sessions, as well as the participants involved.
For organizations that require more advanced session recording and auditing capabilities, TeamViewer offers additional options through its other products. For example, TeamViewer Tensor includes session recording and auditing features, allowing organizations to review and analyze remote support sessions for compliance purposes.
It is important for users and organizations to be aware of the potential privacy and security implications when recording or auditing remote support sessions. Proper consent should be obtained from all parties involved before recording any sessions, and any recorded data should be stored securely and with appropriate access controls.
Remote access and control
Remote access and control is one of the key features offered by TeamViewer QuickSupport. It allows users to remotely connect to and control a device from another location. This feature is particularly useful for providing technical support or troubleshooting issues on a remote computer or mobile device.
With remote access and control, a user can view the screen of the remote device in real-time, manipulate files and settings, and even transfer files between the local and remote devices. This can be done using a variety of devices, including desktop computers, laptops, smartphones, and tablets, making it a versatile tool for remote support.
TeamViewer QuickSupport uses secure encryption protocols to ensure the security of the remote connection. This means that the data transmitted between the local and remote devices is encrypted, making it difficult for anyone else to intercept or access the data. TeamViewer also provides two-factor authentication for added security, requiring users to provide a unique code in addition to their password to access the remote device.
Despite these security measures, there are still some risks associated with remote access and control. One potential risk is the possibility of unauthorized access to the remote device. If the TeamViewer QuickSupport software is installed on a device without the knowledge or consent of the user, it could potentially be used to gain unauthorized access to the device. To mitigate this risk, it is important to ensure that the software is only installed and used on trusted devices.
Another risk is the potential for exploitation of vulnerabilities in the TeamViewer QuickSupport software. Like any software, there is always the possibility of security vulnerabilities being discovered and exploited by malicious individuals. To reduce this risk, it is important to keep the software up to date by regularly installing any updates or patches provided by TeamViewer.
- In conclusion, remote access and control provided by TeamViewer QuickSupport is a convenient and powerful tool for remote support. It offers secure encryption and authentication to protect the privacy and security of the remote connection. However, it is important to be aware of the risks associated with unauthorized access and software vulnerabilities and take necessary precautions to mitigate these risks.
Privacy and data protection
TeamViewer QuickSupport takes privacy and data protection seriously. The application implements several security features to ensure the privacy and protection of user data:
- End-to-end encryption: TeamViewer QuickSupport uses AES 256-bit encryption, which is considered highly secure. This encryption ensures that the data transferred between the user and the client device remains private and protected.
- Two-factor authentication: TeamViewer QuickSupport supports two-factor authentication, which adds an extra layer of security by requiring users to provide a secondary authentication method, such as a unique code sent to their mobile device, in addition to their standard login credentials.
- Access control: The application allows users to control who can access their devices. Users can specify trusted devices and enable or disable remote access as needed.
- Permissions system: TeamViewer QuickSupport provides a comprehensive permissions system, allowing users to define and manage what actions remote users can perform on their device. This helps prevent unauthorized access and ensures that only necessary actions are allowed.
- Session recording: The application does not have the ability to record sessions, ensuring that user activities and data remain private and confidential.
Despite these security features, there are certain risks associated with using TeamViewer QuickSupport:
- Social engineering: Attackers may try to manipulate users into providing access to their devices through social engineering techniques. Users should be cautious of unsolicited requests for remote access and only grant access to trusted individuals or organizations.
- Vulnerabilities: Like any software application, TeamViewer QuickSupport may have vulnerabilities that can be exploited by malicious actors. It is important to keep the application up to date with the latest security patches and to follow best practices for securing systems.
- Trustworthiness of the remote device: When granting remote access to a device, users should ensure that the remote device is secure and trustworthy. Malware or compromised devices can pose security risks and potentially lead to unauthorized access or data breaches.
In conclusion, TeamViewer QuickSupport implements robust privacy and data protection measures, such as end-to-end encryption and access control, to ensure the security of user data. However, users should remain vigilant and follow security best practices to minimize the risks associated with remote access.
FAQ:
What is TeamViewer QuickSupport?
TeamViewer QuickSupport is a remote support software that allows users to provide remote assistance to another computer or device. It can be used to troubleshoot problems, install applications, or perform other tasks remotely.
Is TeamViewer QuickSupport safe to use?
Yes, TeamViewer QuickSupport is generally considered safe to use. It has several security features in place to protect user data and privacy.
What security features does TeamViewer QuickSupport have?
TeamViewer QuickSupport uses end-to-end encryption to secure remote connections. It also has two-factor authentication options and allows users to set up access controls and permissions to ensure only authorized individuals can connect to their devices.
Can someone else access my computer without my permission if I have TeamViewer QuickSupport installed?
No, someone cannot access your computer without your permission if you have TeamViewer QuickSupport installed. The software requires a unique ID and password to establish a remote connection, and you have control over who can access your computer.
Are there any risks associated with using TeamViewer QuickSupport?
While TeamViewer QuickSupport is generally safe, there are some risks to be aware of. If you share your unique ID and password with someone you don’t trust, they could gain unauthorized access to your computer. It’s essential to only provide access to trusted individuals.
Can TeamViewer QuickSupport be used for malicious purposes?
Technically, TeamViewer QuickSupport can be used for malicious purposes if someone gains unauthorized access to your computer. However, with proper security measures in place, such as strong passwords and access controls, the risk of this happening is significantly reduced.
What should I do if I suspect someone has accessed my computer through TeamViewer QuickSupport without my permission?
If you suspect unauthorized access to your computer through TeamViewer QuickSupport, it is recommended to change your TeamViewer password immediately. You should also consider contacting TeamViewer support for further assistance and to report any suspicious activity.