With the introduction of Apple’s Touch ID, unlocking your iPhone with a fingerprint became an everyday convenience. But have you ever wondered where your passwords are actually stored? In this article, we will explore the security measures that Apple has implemented to protect your passwords and understand how they are stored on your iPhone.
First and foremost, it is important to note that Apple takes the security of your passwords very seriously. When you set up Touch ID, your fingerprint is securely stored in a dedicated area of the iPhone’s chip called the Secure Enclave. This is a separate processor specifically designed to handle fingerprint data and protect it from being accessed or tampered with.
In addition to storing your fingerprint securely, Apple also takes steps to ensure that your actual passwords are protected. When you set up Touch ID, your iPhone prompts you to create a passcode as a backup authentication method. This passcode is used to encrypt and protect your passwords, which are stored in the device’s Keychain.
The Keychain is a secure and encrypted database that stores your passwords, credit card information, and other sensitive data. It is protected by encryption keys derived from your passcode, making it extremely difficult for anyone without the passcode to access your passwords.
While the Touch ID sensor itself is very secure, it is worth noting that no security measure is completely foolproof. There have been cases of hackers finding ways to bypass the Touch ID system, although these incidents are extremely rare. It is always a good idea to use complex and unique passwords for additional security, regardless of whether you are using Touch ID or not.
In conclusion, Apple has implemented robust security measures to protect your passwords with Touch ID. Your fingerprints are securely stored in the Secure Enclave, and your passwords are encrypted and stored in the Keychain. While no security measure is perfect, Touch ID and the Keychain provide a strong layer of protection for your sensitive data on your iPhone.
Understanding iPhone Touch ID
iPhone Touch ID is a biometric authentication system developed by Apple Inc. It allows users to unlock their iPhones and make secure transactions using their fingerprints instead of traditional passwords. This technology provides a convenient and secure way to authenticate users and protect their sensitive information.
Touch ID uses a capacitive sensor built into the home button of the iPhone. When a user sets up Touch ID, the sensor captures a high-resolution image of their fingerprint, which is saved locally on the device’s Secure Enclave, a separate part of the iPhone’s processor that stores encrypted data and handles secure operations.
The captured fingerprint image is converted into a mathematical representation called a template. This template is then used to authenticate the user’s fingerprint during the unlocking or transaction process. The template is securely stored on the device and cannot be accessed or extracted by any apps or external sources. It is important to note that Apple does not have access to the fingerprint data.
To ensure security, the Touch ID system employs various techniques to protect against spoofing attacks. These include analyzing both the physical and electrical characteristics of the user’s fingerprints, requiring a live finger for authentication, and regularly updating the fingerprint template to account for changes in the user’s fingerprint over time.
In addition to unlocking the iPhone, Touch ID can also be used for various purposes, such as authorizing Apple Pay transactions, accessing certain apps, and making in-app purchases. Developers can integrate Touch ID into their apps using Apple’s Touch ID API, allowing users to securely authenticate and access their data.
Overall, iPhone Touch ID provides a secure and convenient biometric authentication system that enhances the security of the device and protects user data. With its robust security measures and seamless integration with various applications, Touch ID has become an essential feature for many iPhone users.
The Encryption Behind Touch ID
With the introduction of Touch ID, Apple implemented a secure and efficient encryption system to protect users’ biometric data. This encryption system ensures that the fingerprint information collected by Touch ID is stored securely and cannot be accessed by unauthorized parties.
When a user sets up Touch ID on their iPhone, the device creates a unique key called the “Secure Enclave Key” (SEK). This key is generated based on a variety of factors, including the user’s passcode and the hardware characteristics of the device. The SEK is stored securely in a dedicated security chip called the Secure Enclave, which is isolated from the rest of the device’s hardware.
In addition to the SEK, another key called the “Unique Device Key” (UDK) is also generated during the Touch ID setup process. The UDK is unique to each device and is used to encrypt the fingerprint data before it is stored in the Secure Enclave. This ensures that even if the encrypted data is somehow obtained, it cannot be decrypted without the UDK.
All fingerprint data collected by Touch ID is stored in the Secure Enclave in an encrypted form. The Secure Enclave chip is designed to be tamper-resistant, meaning that it is extremely difficult for an attacker to physically access or extract data from it. The Secure Enclave also enforces a variety of security measures, such as rate limiting and hardware-based encryption, to protect against unauthorized access attempts.
When a user attempts to authenticate with Touch ID, the device compares the fingerprint data obtained from the sensor with the encrypted fingerprint templates stored in the Secure Enclave. This comparison is performed entirely within the Secure Enclave, ensuring that the sensitive biometric data never leaves the chip. If the fingerprint matches, the device is unlocked and the user can access their data.
It is important to note that the encrypted fingerprint data stored in the Secure Enclave is not accessible to the operating system or any other applications running on the device. This ensures that even if a malicious app gains access to a user’s device, it cannot access or manipulate the fingerprint data collected by Touch ID.
In conclusion, the encryption system behind Touch ID ensures that users’ fingerprint data is stored securely and protected from unauthorized access. Apple’s implementation of the Secure Enclave and the use of unique encryption keys provide robust security for biometric authentication on the iPhone.
Securing Your Passwords with Touch ID
With the advent of Touch ID technology on iPhones, users now have the option to secure their device and access various applications using their fingerprints. This technology not only provides convenience but also enhances the security of personal information, including passwords.
When utilizing Touch ID for password storage, the user’s fingerprint data is encrypted and stored securely within the device’s Secure Enclave. This enclave is a separate chip that is designed specifically for secure operations and is isolated from the rest of the system. This ensures that the fingerprint data cannot be accessed by any other applications or components of the device.
When a user sets up Touch ID, their fingerprint is first transformed into a mathematical representation known as a template. This template is then encrypted and stored within the Secure Enclave. The actual fingerprint image is never stored on the device or in any remote servers.
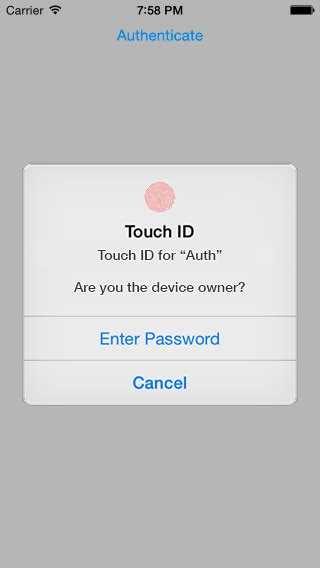
When the user tries to unlock their device or access a password-protected application, their fingerprint is scanned and compared to the stored template within the Secure Enclave. If the fingerprint matches, the device is unlocked, and the user can proceed to use their passwords or access the secured application. If the fingerprint does not match, access is denied, and the user is prompted to enter their passcode for authentication instead.
The use of Touch ID for password storage provides an additional layer of security for users. Even if someone gains physical access to the device, they would still need to provide a matching fingerprint to access the passwords. This makes it significantly harder for unauthorized individuals to gain access to sensitive information.
Furthermore, Touch ID also offers the capability to store multiple fingerprints, allowing authorized individuals such as family members or close friends to unlock the device or access password-protected applications. This feature provides convenience without compromising security.
It is worth noting that while Touch ID provides strong security measures for password storage, it is important for users to take additional precautions to protect their passwords. This includes using strong and unique passwords, enabling two-factor authentication, and keeping the device updated with the latest security patches.
In conclusion, securing your passwords with Touch ID offers a convenient and secure way to access your device and password-protected applications. The encrypted fingerprint data stored within the Secure Enclave ensures that only authorized individuals can access your passwords, providing peace of mind and protection for your personal information.
Touch ID vs. Traditional Passwords
Introduction:
The use of passwords has been the standard method for securing personal devices and online accounts for many years. However, the introduction of Touch ID technology by Apple has provided an alternative method for user authentication and device protection. This article explores the differences between Touch ID and traditional passwords, highlighting their strengths and weaknesses.
Convenience:
- Touch ID: With Touch ID, users can simply place their finger on the device’s fingerprint sensor to unlock it or approve certain actions. This eliminates the need for remembering complex passwords and typing them in every time.
- Traditional Passwords: Traditional passwords require users to memorize and enter alphanumeric combinations, making them more time-consuming and prone to human error or forgetfulness.
Security:
- Touch ID: When properly implemented, Touch ID provides a high level of security by using biometric data unique to each individual. Fingerprints are not easily replicable, making it difficult for unauthorized users to bypass the authentication process.
- Traditional Passwords: While passwords can be strong and secure if properly chosen and managed, they are still susceptible to brute-force attacks, dictionary attacks, and social engineering. Users may also reuse passwords across multiple accounts, potentially compromising their overall security.
Privacy:
- Touch ID: Touch ID data is securely stored on the device’s dedicated Secure Enclave, a separate chip that ensures the proper handling and protection of sensitive information. This means the fingerprint data never leaves the device, providing a higher level of privacy.
- Traditional Passwords: Passwords, especially when used with online accounts, are stored on remote servers, which can potentially be targeted by hackers, leaving users vulnerable to data breaches and identity theft.
Adoption and Compatibility:
- Touch ID: Touch ID technology is currently available on various iPhone models, making it accessible to a significant number of users. However, it is limited to Apple devices and may not be compatible with all apps or systems.
- Traditional Passwords: Traditional passwords are widely adopted and compatible with most devices, platforms, and applications, making them universally accessible.
Conclusion:
While both Touch ID and traditional passwords have their own advantages and disadvantages, the use of biometric authentication, such as Touch ID, offers a more convenient and secure option for device protection and user authentication. However, it is important to note that no security method is foolproof, and both options should be used in conjunction with other security measures to achieve the highest level of protection.
Touch ID and Biometric Data Privacy
In recent years, the use of biometric data, such as fingerprints, has become increasingly prevalent in various technologies, including smartphones. Apple’s Touch ID is one such technology that allows users to unlock their iPhones using their fingerprints. While Touch ID offers convenience and enhanced security, it also raises concerns about biometric data privacy.
Biometric data, including fingerprints, is unique to each individual and can be considered personally identifiable information (PII). As such, the privacy and security of this data are of utmost importance. Apple recognized the sensitive nature of biometric data and took several measures to ensure its protection.
Firstly, when an iPhone user registers their fingerprint with Touch ID, the device creates a mathematical representation, termed a “cryptographic hash,” of the fingerprint. This mathematical representation is stored securely in a hardware-encrypted enclave within the iPhone’s processor, known as the Secure Enclave. The Secure Enclave is designed to be isolated from the rest of the system and inaccessible to other processes, ensuring the confidentiality of the stored biometric data.
Additionally, Apple implemented a strong authentication mechanism for accessing the biometric data stored in the Secure Enclave. This means that only authorized processes, such as the Touch ID authentication subsystem, can access the stored data. Unauthorized access attempts, such as hacking or tampering, are actively prevented through various hardware and software security measures.
Furthermore, Apple ensures that the biometric data is not sent to its servers or stored in the cloud. The entire authentication process, from reading the fingerprint to verifying its match, occurs locally on the device. This approach minimizes the risk of unauthorized access or data breaches through external systems.
To further protect user privacy, Apple has provided developers with strict guidelines on how to handle biometric data in their applications. These guidelines prohibit the storage of biometric data, require the use of encryption when transferring it, and mandate clear user consent for any biometric data usage.
In summary, Touch ID and the storage of biometric data on the iPhone prioritize the privacy and security of user information. Apple employs various technical and policy measures to ensure the confidentiality and integrity of biometric data, keeping it securely stored within the device’s Secure Enclave and eliminating the need for external data transfers. By adhering to strict guidelines and implementing strong authentication mechanisms, Apple aims to safeguard user privacy and maintain the trust of its customers.
Protecting Your Touch ID from Unauthorized Access
Touch ID is a convenient and secure feature on your iPhone that allows you to unlock your device and make purchases with a simple fingerprint scan. To ensure the safety of your Touch ID and protect it from unauthorized access, consider the following measures:
- Place strong emphasis on creating a strong passcode for your device. This passcode should not be easily guessable and should contain a combination of alphanumeric characters.
- Avoid sharing your passcode or Touch ID with anyone, even if they are trusted individuals.
- Enable the “Erase Data” feature, which automatically erases all data on your iPhone after ten failed passcode attempts. This can prevent unauthorized access to your Touch ID.
- Regularly update your iPhone’s operating system and applications to ensure you have the latest security patches and bug fixes.
- Be cautious when installing third-party applications and only download apps from trusted sources, such as the App Store. Unauthorized apps may try to access your Touch ID data.
- Consider using two-factor authentication for your Apple ID. This adds an additional layer of security by requiring a second form of verification, such as a passcode sent to a trusted device.
- If you suspect that your Touch ID has been compromised, you can remove and re-add your fingerprints in the Settings app to ensure only authorized prints are recognized.
By following these guidelines, you can enhance the security of your Touch ID and protect it from unauthorized access.
Can Touch ID be Hacked?
Touch ID is the fingerprint recognition feature introduced by Apple in 2013 with the iPhone 5S. It allows users to unlock their devices and authorize payments using their fingerprints. While it is a convenient way to secure your iPhone, the question remains: Can Touch ID be hacked?
Apple has implemented various security measures to protect Touch ID from being hacked. Here are some of the reasons why Touch ID is considered to be a secure authentication method:
- Fingerprint matching: Touch ID uses a biometric sensor to capture and analyze the unique patterns of your fingerprint. It compares the captured fingerprint with the enrolled fingerprint data stored securely on the iPhone’s Secure Enclave, a dedicated chip that provides a high level of security.
- Secure Enclave: The Secure Enclave is a separate processor within the iPhone that stores encrypted fingerprint data. It is isolated from the main processor and operating system, making it difficult for hackers to gain unauthorized access to the stored data.
- Encryption: Touch ID data is encrypted, both in transit and at rest, to further protect it from being compromised.
- False positives: Touch ID is designed to minimize the possibility of false positive readings. The sensor requires live fingerprints, preventing hackers from using lifted or reproduced fingerprints.
While Touch ID is generally considered to be secure, it is not entirely foolproof. There have been instances where researchers have been able to bypass Touch ID using advanced techniques, such as creating fake fingerprints or using high-resolution images of fingerprints. However, these methods usually require significant expertise and resources, making them unlikely to be used by the average hacker.
It is worth noting that Apple regularly updates its security measures to address any vulnerabilities that may be discovered. By keeping your iPhone’s operating system up to date, you can ensure that the latest security patches are installed, further reducing the risk of Touch ID being hacked.
In conclusion, while Touch ID is generally secure, it is important to remember that no security measure is 100% foolproof. It is always recommended to use strong passcodes in addition to Touch ID for an added layer of security.
Final Thoughts on Touch ID Security
In conclusion, the security of Touch ID on iPhone is a complex topic. While it offers a convenient and fast way to unlock your device and authenticate with certain apps and services, it is not without its potential risks.
It is important to remember that Touch ID is not foolproof and can be bypassed in certain situations. For example, if someone is able to obtain a high-resolution fingerprint image or a 3D model of your fingerprint, they could potentially create a fake fingerprint that can fool the sensor.
Additionally, it is worth noting that Touch ID is only as secure as the passcode or password that is used as a backup. If someone is able to guess or obtain your passcode, they may be able to bypass the Touch ID authentication altogether.
Despite these potential risks, Touch ID still provides an additional layer of security compared to simply using a passcode or password. The ability to use biometric data for authentication adds an extra level of complexity for potential attackers.
Furthermore, Apple has implemented various security features and measures to protect the privacy and security of Touch ID. For example, fingerprint data is stored locally on the device and is encrypted, making it extremely difficult for anyone to access or replicate the data.
In conclusion, while Touch ID may not be completely infallible, it is a valuable and convenient security feature that can help protect your device and personal information. It is important to keep in mind that no security measure is perfect, and using a combination of strong passwords, passcodes, and biometric authentication can provide the strongest level of security.
FAQ:
How does Touch ID work on the iPhone?
Touch ID on the iPhone works by using a fingerprint sensor embedded in the device’s home button. When a user registers their fingerprint, the data is encrypted and stored in a secure enclave within the device’s processor. When the user touches their finger to the home button, the fingerprint is compared to the stored data in order to authenticate the user.
What happens if someone tries to access my iPhone with Touch ID?
If someone tries to access your iPhone with Touch ID and fails to provide a valid fingerprint, the device will prompt for a passcode instead. This ensures that unauthorized users cannot bypass the security of the device by simply attempting to use different fingerprints.
Where are the passwords stored on an iPhone with Touch ID?
The passwords on an iPhone with Touch ID are not stored directly. Instead, the device uses a system called keychain to securely store passwords and other sensitive data. The keychain is encrypted and can only be accessed by authorized processes within the iOS operating system.
Is Touch ID on the iPhone secure?
Touch ID on the iPhone is generally considered secure. The fingerprint data is encrypted and stored in a secure enclave, which makes it difficult for unauthorized users to access. Additionally, the use of a passcode as a backup authentication method adds an extra layer of security.