In recent years, torrenting has become a popular way to share and download files online. However, many countries and internet service providers (ISPs) have started blocking access to popular torrent websites due to copyright infringement concerns. This can be frustrating for users who rely on torrents to access restricted content or share files.
Fortunately, there are several ways to bypass these torrent blocks and gain access to restricted content. One method is to use a virtual private network (VPN). A VPN encrypts your internet connection and routes it through a server in a different location, effectively masking your IP address and bypassing any restrictions put in place by your ISP or government.
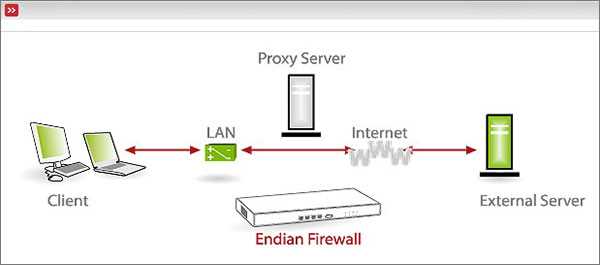
Another option is to use a proxy server. A proxy server acts as a middleman between you and the internet, allowing you to access restricted content by masking your IP address. Proxies can be set up in your browser settings or through third-party software. While proxies can be a quick and easy solution, they may not always provide the same level of security as a VPN.
In addition to VPNs and proxy servers, there are also alternative torrenting methods that can help bypass restrictions. One such method is using magnet links instead of traditional torrent files. Magnet links contain all the necessary information to initiate a download and can be shared via websites or social media platforms. By using magnet links, users can bypass torrent blocks and access restricted content without relying on specific torrent websites.
While torrent blocks can be frustrating, there are solutions available for users looking to bypass restrictions and access restricted content. Whether it’s using a VPN, proxy server, or alternative torrenting methods, these options can help ensure that users have access to the content they need.
Methods to Evade Torrent Restrictions and Reach Limited Content
If you find yourself unable to access certain content due to torrent restrictions, there are several methods you can employ to bypass these limitations and access the restricted content.
1. Use a VPN (Virtual Private Network)
One of the most effective ways to bypass torrent blocks is by using a VPN. A VPN encrypts your internet connection and routes it through a server located in a different country. This hides your IP address and makes it appear as if you are accessing the content from a different location, allowing you to bypass restrictions.
2. Seedbox
A seedbox is a remote server specifically designed for downloading and uploading torrents. By using a seedbox, you can download the torrents directly to the server without affecting your personal internet connection. Once the torrent is downloaded to the seedbox, you can easily transfer the files to your device using a secure connection.
3. Proxy Servers
Proxy servers act as intermediaries between your device and the internet. They can help you access restricted content by masking your IP address and routing your internet traffic through a different location. However, proxy servers may not provide the same level of security and privacy as VPNs.
4. Tor Network
The Tor network is a decentralized network that allows users to browse the internet anonymously. By using the Tor network, you can bypass torrent blocks and access restricted content. However, the Tor network may not be as fast as other methods and can be more complex to set up.
5. Cloud Torrenting
Cloud torrenting involves using a cloud-based torrent client to download and manage your torrents. This method allows you to bypass torrent blocks by downloading the torrents directly to the cloud server. Once the torrents are downloaded, you can easily access the files from any device with an internet connection.
6. Usenet
Usenet is an older but reliable method for file sharing. It operates on a different protocol than torrents and allows users to download files from dedicated servers. Usenet provides a high level of security and privacy, making it an effective way to bypass torrent restrictions and access restricted content.
With these methods at your disposal, you can evade torrent restrictions and gain access to restricted content. However, it’s important to note that torrenting copyrighted material may be illegal in some jurisdictions. Always ensure that you are using these methods to access legal and authorized content.
Virtual Private Networks (VPNs)
A Virtual Private Network (VPN) is a powerful tool that allows users to bypass torrent blocks and access restricted content. It works by creating a secure and private connection between the user’s device and the internet. By using a VPN, all internet traffic is encrypted and routed through a server located in a different geographic location. This makes it appear as if the user’s device is located in a different region, allowing them to access content that is otherwise blocked or restricted.
There are several advantages to using a VPN:
- Security: VPNs provide a high level of security by encrypting internet traffic, making it difficult for hackers or government agencies to intercept or monitor online activities.
- Anonymity: VPNs hide the user’s IP address, making it difficult for websites or online services to track their online activities or identify their location.
- Access to restricted content: VPNs can bypass geo-restrictions, allowing users to access content that is blocked in their country or region. This is particularly useful for accessing streaming services, such as Netflix or Hulu, which may have different libraries in different regions.
- Bypassing torrent blocks: Many internet service providers (ISPs) block access to torrent websites or throttle download speeds for torrent traffic. By using a VPN, users can bypass these restrictions and access torrent sites without any issues.
When choosing a VPN, it’s important to consider factors such as speed, server locations, and privacy policy. Some popular VPN services include NordVPN, ExpressVPN, and CyberGhost. These services offer a range of features and pricing options to suit different needs.
| VPN Service | Features | Price |
|---|---|---|
| NordVPN | High-speed servers, strict no-logs policy, advanced security features | $11.95/month |
| ExpressVPN | Wide server network, easy-to-use apps, unlimited bandwidth | $12.95/month |
| CyberGhost | Optimized servers for streaming and torrenting, user-friendly interface | $12.99/month |
It’s worth noting that while VPNs are a powerful tool for bypassing torrent blocks and accessing restricted content, they may not always be 100% effective. Some websites or online services have implemented more advanced detection techniques that can identify and block VPN traffic. In such cases, it may be necessary to try different VPN providers or explore alternative methods, such as proxy servers or Tor network.
Overall, Virtual Private Networks (VPNs) are a reliable and effective way to bypass torrent blocks and access restricted content. With the right VPN service, users can enjoy a secure and unrestricted internet experience, while preserving their privacy and anonymity.
Proxy Servers for Torrents
Proxy servers can be used to bypass torrent blocks and access restricted content. By connecting to a proxy server, your torrent traffic is routed through a different IP address, allowing you to hide your real IP and location.
Here are some popular proxy server options for torrents:
-
VPN Proxies: Virtual Private Networks (VPNs) offer encrypted connections and a high level of anonymity. Many VPN providers offer dedicated torrent servers that optimize your connection for P2P file sharing.
-
Web-based Proxies: These proxies can be accessed through web browsers and require no installation. Simply enter the torrent URL or magnet link into the proxy website, and it will fetch the file for you.
-
SOCKS Proxies: SOCKS (Socket Secure) proxies can handle any type of internet traffic, including torrents. They operate at a lower level and can be set up within torrent clients or network settings.
-
Tor Network: The Tor network is known for its anonymity features. Using torrent clients with the Tor network can provide added privacy, but it may result in slower download speeds due to the multiple hops your traffic goes through.
It is important to note that when using proxy servers for torrents, you should choose a reputable and reliable provider. Some proxy servers may log your activity or offer poor connection speeds. Always read reviews and consider the privacy policies of the proxy service before using it.
Additionally, it is crucial to check the legality of torrenting in your country or region. While using proxy servers can help bypass restrictions, it is essential to abide by local laws and regulations.
| Pros | Cons |
|---|---|
|
|
Overall, proxy servers can be a useful tool for accessing restricted content and bypassing torrent blocks. However, it is important to consider the limitations and potential risks associated with using proxy servers for torrents. It is always recommended to prioritize your privacy and security when engaging in torrenting activities.
Tor Network for Bypassing Blocks
If you’re facing restrictions on accessing certain websites or content due to internet censorship or blocking by your ISP or government, the Tor network can be an effective solution to bypass these blocks and access restricted content. Tor, short for “The Onion Router,” is a network of servers that allows users to browse the internet anonymously by routing their traffic through a series of encrypted tunnels.
How Tor Works
Tor works by encrypting and routing your internet traffic through a network of volunteer-operated servers called “nodes” or “relays”. When you access a website through Tor, your traffic is bounced through multiple relays, making it difficult for anyone to track your online activities or identify your IP address.
Using Tor to Bypass Torrent Blocks
If your ISP or government is blocking access to torrent websites, you can use Tor to bypass these blocks and access the content you want. Here’s how:
- Download and install the Tor Browser, which is a modified version of the Mozilla Firefox browser that’s specifically designed to work with the Tor network.
- Launch the Tor Browser and connect to the Tor network.
- Once connected, you can access torrent websites and download content anonymously.
Advantages and Disadvantages of Using Tor
Using the Tor network has both advantages and disadvantages:
- Advantages:
- Anonymous browsing: Tor hides your IP address and makes it difficult for anyone to track your online activities.
- Bypassing censorship: Tor can help you access blocked websites and content.
- Security: Tor encrypts your traffic, making it more secure against surveillance and interception.
- Disadvantages:
- Slower browsing speed: Because your traffic is routed through multiple relays, browsing speed can be slower compared to a regular internet connection.
- Potential privacy risks: While Tor provides anonymity, it’s important to note that the exit node, the final relay in the network, can potentially see your unencrypted traffic.
- Not suitable for all online activities: Tor is best suited for browsing the web and accessing blocked content, but it may not be ideal for tasks such as streaming high-definition videos or online gaming.
Conclusion
The Tor network is a powerful tool for bypassing blocks and accessing restricted content. By encrypting and routing your internet traffic through a network of relays, Tor allows you to browse the web anonymously and access blocked websites. However, it’s important to be aware of the limitations and potential risks associated with using Tor. Consider your specific needs and circumstances before deciding to use Tor as a solution for bypassing blocks.
Seedbox Services for Safe Torrenting
If you are a torrent enthusiast, you may have come across situations where your access to torrent sites has been blocked or limited by your internet service provider or government regulations. In such cases, using a seedbox can be a great solution to bypass these restrictions and ensure safe torrenting.
A seedbox is a remote server that allows you to download and upload torrents at high speeds. It acts as a middleman between you and the torrent sites, making it difficult for anyone to track your online activities. Here are some reasons why using a seedbox is beneficial for safe torrenting:
- Enhanced Privacy: When you use a seedbox, your IP address is completely masked. This means that your internet service provider or any other monitoring party cannot track your online activities or link them to your real identity.
- High Speeds: Seedboxes are usually hosted on servers with high bandwidth connections. This allows for faster downloading and uploading speeds compared to your personal internet connection.
- No Bandwidth Limitations: Unlike your personal internet connection, seedboxes often come with unlimited bandwidth. This means that you can download and upload torrents as much as you want without worrying about hitting any data caps.
- Remote Access: Seedboxes are accessed through a web interface, which means you can manage your torrents from anywhere with an internet connection. This allows you to start, stop, or delete torrents remotely without exposing your home IP address.
- Security and Anonymity: Seedboxes often come with additional security features, such as encrypted connections and VPN support. This ensures that your torrenting activities are completely anonymous and protected from any potential cyber threats.
When choosing a seedbox service, it is important to consider factors such as server location, storage capacity, pricing, and customer support. Additionally, it is advisable to opt for a seedbox service that supports popular torrent clients and provides a user-friendly interface.
In conclusion, seedbox services offer a safe and efficient way to bypass torrent blocks and access restricted content. By using a seedbox, you can enjoy fast and secure torrenting without the risk of exposing your real IP address or facing any bandwidth limitations.
Utilizing Cloud Downloaders
Cloud downloaders are online services that allow you to download files from various sources, including torrents. These services act as intermediaries between your computer and the torrent network, allowing you to access and download files without directly connecting to the torrent network.
Here are some advantages of utilizing cloud downloaders:
- Access to restricted content: Cloud downloaders can help you bypass torrent blocks and access content that is otherwise restricted in your country or network.
- Increased privacy: By using a cloud downloader, your IP address and online activities are not directly exposed to the torrent network, providing an additional layer of privacy and security.
- Faster and more reliable downloads: Cloud downloaders often have high-speed servers that can download files faster than your regular internet connection. Additionally, these services can handle unstable or slow torrent connections, resulting in more reliable downloads.
- No need for torrent client: With cloud downloaders, you don’t need to install a torrent client on your computer. All the downloading and file management is done through the online interface of the service.
While there are several cloud downloaders available, most of them work in a similar way:
- Find a cloud downloader service: Search for a reputable cloud downloader service that suits your needs. Popular services include Bitport.io, ZbigZ, and Filestream.
- Sign up for an account: Create an account on the chosen cloud downloader service. Some services offer free accounts with limited features, while others require a subscription.
- Copy the torrent link: Find the torrent file or magnet link for the content you want to download. Copy the link to your clipboard.
- Paste the torrent link: Go to the cloud downloader service and paste the torrent link into the provided field or upload the torrent file.
- Start the download: Depending on the service, you may need to select a storage location or adjust some settings before starting the download. Once everything is set, start the download.
- Wait for the download to complete: The cloud downloader will handle the downloading process, and you can monitor the progress through the online interface. Once the download is finished, you can usually download the file to your computer or directly access it through the service.
Keep in mind that while cloud downloaders provide a convenient way to access and download torrent content, they are not foolproof. Some services may have limitations on file size, download quotas, or access to certain torrent websites. Additionally, using cloud downloaders for copyright-infringing content may not be legal in your jurisdiction, so make sure to use these services responsibly and within the boundaries of the law.
DNS Changing to Unblock Torrents
If you are facing restrictions on accessing torrent websites, changing your DNS (Domain Name System) settings can help you bypass these blocks and regain access to the content you want.
DNS is responsible for translating domain names (such as www.example.com) into IP addresses that computers understand. By changing your DNS settings, you can route your internet traffic through different DNS servers, potentially bypassing any blocks implemented by your internet service provider (ISP) or government.
Here are the steps to change your DNS settings:
- Identify a suitable DNS server: There are several free DNS services available, such as Google Public DNS, OpenDNS, and Cloudflare. Research and choose a reliable DNS server that is known for its speed and security.
- Access your network settings: Open the network settings on your device. The process may vary depending on your operating system (Windows, macOS, iOS, Android) and device type.
- Find the DNS settings: Look for the DNS settings or DNS server options in your network settings. It is usually found under the internet or network configuration section.
- Enter the new DNS server: Replace the existing DNS server addresses with the IP addresses of the DNS server you have chosen. Some DNS services provide primary and secondary DNS server addresses, while others may only provide one.
- Save the changes: After entering the new DNS server addresses, save the changes and exit the network settings.
Once you have changed your DNS settings, your device will start using the new DNS server to resolve domain names. This can help you bypass any censorship or blocks imposed on torrent websites, as your requests are now being processed through a different DNS server. However, please note that changing DNS settings may affect your browsing experience and internet speed, so it’s important to choose a reliable and fast DNS server.
Remember to abide by the laws and regulations in your country regarding torrenting and accessing restricted content. While changing DNS settings can help you bypass blocks, it’s important to use this knowledge responsibly and within legal boundaries.
Tunneling Techniques for Torrent Access
When faced with torrent blocks and restrictions, there are various tunneling techniques that can be used to gain access to the content you desire. These techniques work by routing your internet traffic through encrypted tunnels, thereby bypassing any restrictions put in place by your internet service provider or governmental authorities.
Here are some popular tunneling techniques for torrent access:
-
Virtual Private Networks (VPNs): VPNs are one of the most common and secure methods to bypass torrent blocks. They create a secure connection between your device and a remote server, encrypting your traffic and masking your IP address. By connecting to a VPN server in a country where torrenting is not restricted, you can access torrent sites and download content without any issues.
-
Proxy Servers: Proxy servers act as intermediaries between your device and the internet. They allow you to route your traffic through a server located in a different location. By using a proxy server, you can change your IP address and access torrent sites that may be blocked in your region. However, proxies are less secure than VPNs and may not provide encryption for your traffic.
-
Tor Network: The Tor network is a decentralized network of servers that can be used to anonymize internet traffic. By using the Tor browser, you can access torrent sites and download content without revealing your IP address. However, it is important to note that the Tor network can be slower than other tunneling techniques due to the additional encryption and routing layers involved.
-
SSH Tunnels: SSH (Secure Shell) tunnels can be used to create an encrypted connection between your device and a remote server. By setting up an SSH tunnel, you can route your torrent traffic through the server and bypass any blocks or restrictions. However, SSH tunnels may require technical expertise to set up correctly.
-
VPN Over Tor: This technique combines the use of both a VPN and the Tor network for enhanced privacy and security. By connecting to a VPN server and then routing your traffic through the Tor network, you can further obfuscate your activities and access torrent sites without revealing your IP address.
It is important to note that while these tunneling techniques can help you bypass torrent blocks and access restricted content, they may not be legal in all jurisdictions. It is advisable to consult local laws and regulations regarding internet usage and torrenting before utilizing these techniques.
Utilizing Web Browsers with Built-in VPNs
One effective way to bypass torrent blocks and access restricted content is by using web browsers with built-in VPNs. A Virtual Private Network (VPN) allows you to create a secure connection to another network over the Internet, making it appear as if you are browsing from a different location.
Many popular web browsers now offer built-in VPN services that can be easily activated by users. Some of the most well-known web browsers with built-in VPNs include:
- Opera: Opera is a web browser that comes with a free, unlimited VPN. It allows you to select a virtual location from various countries, making it an ideal choice for bypassing torrent blocks and accessing restricted content.
- Firefox: Mozilla Firefox has a built-in feature called Firefox Private Network that provides a secure VPN connection. However, it is worth noting that this feature is currently only available to users in the United States.
By utilizing web browsers with built-in VPNs, you can easily bypass torrent blocks and access restricted content without the need for additional software or subscriptions. These browsers provide a convenient and user-friendly way to protect your privacy and access the internet freely.
It is important to keep in mind that while a built-in VPN can help you bypass certain restrictions, it may not provide the same level of anonymity and security as a dedicated VPN service. If privacy is a primary concern, it is recommended to consider using a dedicated VPN service.
FAQ:
What is torrent blocking and why is it done?
Torrent blocking is the act of restricting or prohibiting access to torrent websites or files. It is done by internet service providers (ISPs) or government authorities in order to prevent copyrighted content from being illegally shared and downloaded.
Is it legal to bypass torrent blocks?
Bypassing torrent blocks itself is not illegal. However, using torrents to download copyrighted material without proper authorization is illegal in many countries.
What are some common methods to bypass torrent blocks?
There are several methods to bypass torrent blocks. One of the most common methods is to use a virtual private network (VPN) to encrypt and redirect internet traffic. Other methods include using proxy servers or Tor network, changing DNS settings, or accessing torrents through magnet links.
Can using a VPN affect internet speed?
Using a VPN can sometimes have a slight impact on internet speed due to the encryption and rerouting of internet traffic. However, with a reliable and fast VPN service, the impact is usually minimal and may not be noticeable in regular browsing or streaming activities.
Are there any risks involved in bypassing torrent blocks?
While bypassing torrent blocks itself is not risky, there are some potential risks associated with downloading torrents. These risks include downloading malware or viruses, encountering fake or malicious torrents, or facing legal consequences for downloading copyrighted material.